Follow up post about UPS_Invoice trojan
July 15, 2008 14 Comments
I’ve now had a chance to take a slightly closer look at the four copies of this Trojan Agent HFU that I received in the last 24 hours, as discussed in my previous post here. I’ve posted some details of file names and sizes along with MD5 hashes for people to be able to compare their versions against.
The first one which had the half German subject line was a file called UPS_Invoice_317.zip which was 5,420 bytes in size. This one expanded into two levels of folder as UPS_Invoice_317\Ups_invoice\UPS_INVOICE.exe (this was the only one to use lower case in its folder names). The executable was exactly 8,192 bytes (almost certainly padded) and had an MD5 hash of 6B4EF50E3E21205685CEA919EBF93476 which is the same as the one posted by Kayrac on the broadbandreports.com forum. Unfortunately he did not say what the name of the containing zip file was.
My next one was called UPS_INOICE_107.zip (note the mis-spelling) and extracted as UPS_INOICE_107\UPS_INVOICE_107.exe – only one level of folders this time, and the executable inherited the numeric part in its name. The mis-spelling almost certainly came from a mis-spelled folder used to compress it in the first place, as most zip programs default to using the folder name for the zip file as well. This file was only 6,656 bytes long and had MD5 checksum of 0C0F2CB1DEB11EC0AA68DEE0933FAACF. Since this is smaller than all the others I am certain it is a significantly different variant, or perhaps is simply broken. Hopefully I can test this later to see what (if anything) it does.
My third and fourth received emails were both called UPS_INVOICE_107.zip and extracted to UPS_INVOICE_107\UPS_INVOICE_107.exe, both 8,192 bytes long and with the same MD5 digest of 58AC24B1F802990387870D3A5CC2312B. The two zip files however were different sizes (4,117 and 4,178 bytes), so they were not direct copies of one another.
All the files made reference to a Russian domain which was registered on the 11th June. I have obscured the domain name and parts of the IP address in the screenshot below, taken from DNSstuff.com
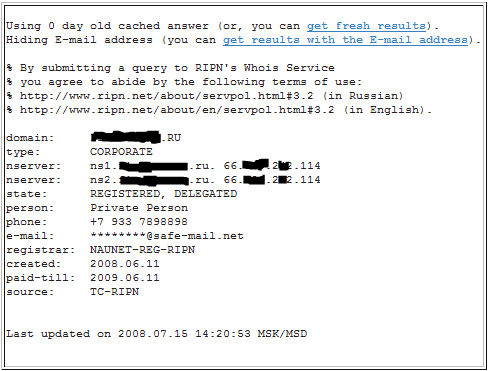
There seems to be an SMTP server running on the same IP as the name servers, presumably to enable the malware to forward copies of itself, or perhaps to send messages home, since it does not seem to be set up to permit relaying.
Anyone have any further information about what this does yet? I’m just setting up a sandbox machine to try and track its infection in a safe environment.
Also, if you have any MD hashes which are different it might be interesting to post them as comments so we see how many flavours of this are out there.
Incidentally, I just noticed that the icon for the executable extracted from the zip file is a pretty crude copy of a Word document icon. Looks like a poor screenshot was used to crop it from.
Running the executable on Vista SP1 as a normal user and with UAC enabled did not seem to do anything – the application crashed out.
I had a process monitor trace and network monitor running, and found nothing written to registry or disk and no traffic generated, other than network traffic to watson.microsoft.com when it attempted to report the application crash. My firewall was configured to block and log all outbound traffic during the test and nothing showed up there either.
Next I need to test it on one my older non-Vista machines to see how they hold up.
Note again, I deliberately ran this while logged in as a non-admin user – I was half expecting a UAC prompt, but instead the malware just fell over, and was unable to replace userinit.exe as others have reported since this is in the protected windows\system32 folder.
1-0 for Vista security today.
Man this one is a real nasty. I had a user open this one. It opens/installs a program called Windows Anti-Virus and tells the user they are infected with 200 virus’. Symantec Endpoint Protection was telling me Trojan.Pandex was on there and all other sorts of crap. Symantec removed about 200 files from various /Windows dirs. SDFix *seems* to have cleaned it up but i still have my doubts.
oh yea some other files it dropped:
tcpsr.sys
lph[random chars].bmp
lph[random chars].exe
ip6fw.sys
its a mass-mailing worm. I had Internet Email Protect fill up the screen with outgoing email scans.
more things recognized by Symantec:
Trojan.Blusod
Joke.Blusod
My computer has been attacked too… Unfortunately we were waiting for some stuff to arrive via UPS so there you go…
My Avast! 4.8 helped me wonderful but I had to delete some bad files from the registry. The malware was responsible for downloading the earlier mentioned XP Antivirus program (which was pretty hard to kill) and destroyed my desktop (i.g. wallpaper). It has left me with no choice of setting to adjust the wallpaper except for standard XP blue look. Has anyone got any ideas how to reset this and have my wallpaper back? I’ve removed files that were spread by the virus from the HKEY_CURRENT_USER registry regarding the false wallpaper setting (including a file called wallpaper.exe which had similar features to the others files (rhuc9u1j0e33v.exe etc).
I would really appreciate anyones help in this matter!
There are reg keys that need to be re-entered after cleaning up the worm.
check out this link:
http://www.precisesecurity.com/threats/trojanblusod/
My cleaning used a mix of SDFix, Avenger (to kill some stubborn files), and Symantec Endpoint v11.
what a pain in teh ass 🙂
I received this Email. Unfortunately, I missed all the usual warnings (like the bad return Email address) and eventually clicked on the .Exe. When nothing happened, it suddenly struck me that I screwed up. I am trying to research how to get rid of this virus/malware.
My only saving grace, if it this indeed sends out mass Emails, is that I use Thunderbird as my Email client and usually these viruses attack Outlook.
Thnx The420Kid! I’m going to try and fix it, but is since I’m not a computer-expert it is going to be difficult for me… Thnx anyway!
INfection started with:
UPS_INVOICE_978172.exe in a zip file.
Attached to an email as described above in the thread.
Likely it has spawned:
C:\WINDOWS\system32\ntos.exe Win32/PSW.Agent.NIF trojan
Infected:
C:\WINDOWS\system32\drivers\beep.sys
C:\WINDOWS\system32\buritos.exe
C:\WINDOWS\buritos.exe
C:\WINDOWS\system32\braviax.exe
C:\WINDOWS\braviax.exe
more spawned files: (sorry no location info)
karina.dat
cru26???.dat
It tried to contact
hxxp://xpsecuritycenter.com/install/Installer.exe
Cleaned it by starting windows xp in Safe Mode
ESET’s NOD32 commandline scanner detected ‘m, I removed ‘m manually.
Hope this helps any of you a little further.
In the last hour I found in my inbox a variation on the UPS_Invoice trojans of last week. This new email claimed to be from “Customs Service” with the subject “Customs – We have received a parcel for you”
Hey, if you could forward me the actual URL that this thing is trying to phone home to, I’d sure appreciate it. We’ve had a few machines compromised, and I’d like to add the address to outbound block on the firewall. Thanks!
My computer got infected with this trojan and now I can’t even log into Windows! Any ideas on how to clean this up without having to re-format my whole hard drive? Thanks!
Also, how do I get into my DOS prompt with Windows XP Home Edition when I can’t even log into Windows?
Gloin
Others have reported the domain name now, but it has been taken down, so no need to block at your gateway, although that can be a useful method of protecting your users and your network, especially in cases like this where the email trojan was only the first part of the problem, it is the other malware it downloads which is even nastier and harder to get rid of (such as XPAntivirus 2008).
You would of course need to consider how to protect users with laptops if they can use these on other unprotected web connections (or rather not protected by you and your filtering rules) such as at home, internet cafes and so on.
Barb
You might be best off with some form of bootdisk such as BartPE or Knoppix which can help you to go through your hard drive and remove files without being logged in to the machine through windows. Alternatively, hit F8 at startup for a menu and see if you have any luck getting in using Safe Mode.
If you get the trojan then use Spybot. It picks it up no problem.